TLDR¶
• Core Points: A developer’s journey from using raw syscalls to understanding NSS and libc, balancing experimental boldness with practical reliability.
• Main Content: Personal narrative of kernel-level experimentation, challenges with libc/NSS, and lessons learned for robust Linux tooling.
• Key Insights: Direct kernel interfacing exposes limits of portability and maintenance; standard C libraries and NSS provide essential abstractions.
• Considerations: Safety, security, and compatibility must guide low-level approaches; documentation and testing are crucial.
• Recommended Actions: Embrace abstractions when appropriate, document experiments, and invest in understanding libc and NSS interfaces for real-world reliability.
Content Overview¶
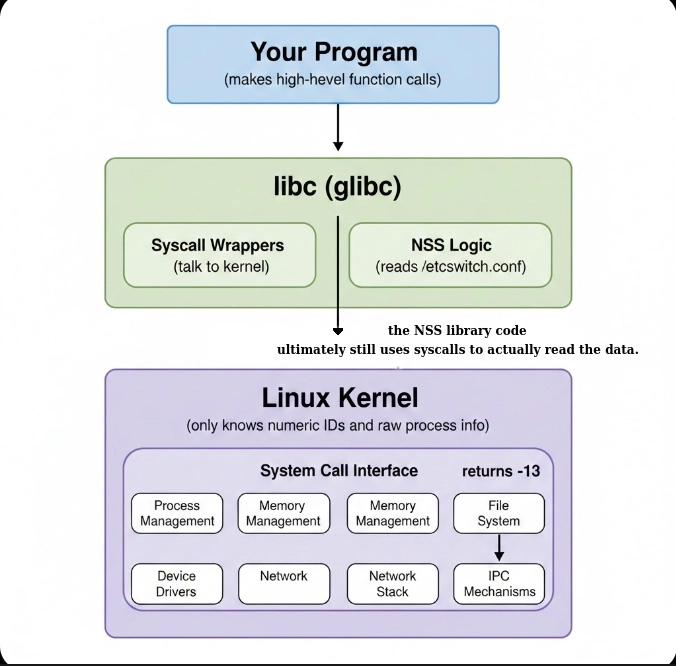
This article recounts a Linux enthusiast’s deep dive into the system, starting with an appetite for low-level experimentation. The author describes building tools that bypass standard C libraries and interface with the kernel directly through raw syscalls. By creating custom headers, implementing bespoke print routines, and performing filesystem interactions via getdents64, the journey traverses process discovery through /proc and directory enumeration without relying on conventional user-space libraries. The narrative reflects an initial confidence in “the real way” of doing things—writing code that talks straight to the kernel—and the practical successes that followed. However, it also acknowledges that such bold approaches come with a set of significant trade-offs, especially when broader compatibility, maintainability, and long-term stability are considered. The article sets up a broader discussion about the evolving understanding of how NSS (Name Service Switch) and libc (the standard C library) shape the Linux user-space experience, and why abstraction layers still matter even for committed kernel enthusiasts.
In-Depth Analysis¶
The author’s early experiments embody a classic developer impulse: push the boundaries of what’s possible by skipping abstractions and going straight to the source of truth—the kernel. Writing tools that perform syscalls directly, crafting custom headers, and implementing basic output routines without relying on the standard C library demonstrate a fearless, curiosity-driven approach. Tools that read directories with getdents64 and parse /proc for process information can, in principle, work with a minimal set of dependencies. In this raw mode, the user interfaces with Linux as a living system rather than as a packaged user-space environment.
Yet, the practical reality soon reveals the limits of this approach. Linux is a complex ecosystem where the kernel, libc, and NSS work together to provide a stable, portable interface to system resources. The libc library exists not merely as convenience but as a compatibility layer that encapsulates system calls, data structures, and calling conventions across different distributions and architectures. NSS, on the other hand, centralizes name resolution and user/group information sources, orchestrating interactions with files such as /etc/passwd, LDAP/RADIUS/Winbind backends, and other services. When one bypasses libc and NSS, several challenges emerge:
Portability: Direct syscalls can vary across kernel versions and architectures. What works on one system may break on another, even with the same kernel version. libc provides a stable ABI that absorbs certain changes and presents a uniform interface to user-space applications.
Maintenance: Custom interfaces require ongoing maintenance to align with evolving kernel interfaces and behavior. The absence of standardized, well-tested wrappers increases the risk of subtle bugs and undefined behavior.
Interoperability: Many system services and development environments assume the presence of libc and NSS. Tools that operate outside these abstractions may fail to interact correctly with typical user-space processes, daemons, and services.
Security and correctness: Bypassing established libraries can complicate security considerations, promise fewer safety checks, and make misuse more likely. libc and NSS incorporate vetted patterns for memory management, error handling, and privilege separation that are easy to overlook when rolling a bespoke solution.
The narrative does not dismiss the value of low-level experimentation; rather, it highlights a learning arc. Early successes—such as successfully opening directories, listing processes, and parsing system-provided information with minimal dependencies—illustrate what is possible with a keen understanding of the kernel’s surface. However, the broader Linux ecosystem’s expectations for stability, compatibility, and correctness strongly reinforce the value of leveraging standard interfaces.
A key takeaway relates to the balance between courage and conservatism in software development. Bold exploration is essential for innovation, but it should be complemented by an appreciation for the layers that standard tooling provides. The journey toward understanding NSS and libc is not simply about accepting these abstractions as “necessary evils”; it’s about recognizing their role in ensuring predictable behavior, security, and long-term viability of software that runs on Linux systems.
When examining NSS and libc more deeply, several practical implications come into focus:
libc as a portability layer: The standard C library abstracts away a large portion of kernel-specific details. It handles platform differences, provides consistent memory management patterns, and offers robust I/O facilities. Learning how libc maps to syscalls, handles errors, and collaborates with the kernel is essential for any developer who writes user-space software that interacts with low-level system resources.
NSS as a flexible resolver: Name resolution and identity services are not a single monolithic mechanism; they are a composite of modules and backends. Understanding NSS involves knowing how the system consults files like /etc/nsswitch.conf, how name services are ordered, and how external sources (LDAP, DNS, etc.) influence the identity of users and groups. This understanding is critical for debugging authentication, authorization, and access control behaviors in complex environments.
The value of standard interfaces: Even in educational or experimental contexts, relying on established APIs helps ensure that the resulting software is robust, portable, and easier to share with others. It lowers the barrier to collaboration and reduces the risk of creating brittle, single-system tools.
The author’s reflection, while rooted in a personal, hands-on exploration, points to broader themes in systems programming. The kernel’s raw power invites experimentation, but the ecosystem’s abstractions—libc, NSS, and related user-space services—exist to ensure reliability, consistency, and security. Recognizing when to lean into the kernel and when to lean on standard libraries is a nuanced judgment call, often refined through experience and concrete use cases.
This journey also emphasizes the importance of documentation and incremental learning. Recording experiments, outcomes, and the rationale for choosing one approach over another creates a valuable knowledge base that can guide future projects. It also helps others understand the trade-offs involved in bypassing conventional tooling, and it offers a blueprint for migrating from experimental codepaths toward production-ready implementations that integrate smoothly with the broader Linux ecosystem.
Perspectives and Impact¶
The evolution from raw syscalls to an appreciation for NSS and libc reflects a broader trajectory in systems programming: from the adrenaline of direct kernel interaction to the pragmatism of stable, maintainable software ecosystems. This journey influences several dimensions:
*圖片來源:Unsplash*
Educational value: For learners, experimenting with raw interfaces can be an effective way to grasp kernel concepts, syscall conventions, and the data flows between user space and kernel space. It builds intuition about performance, bottlenecks, and failure modes that higher-level abstractions sometimes obscure.
Practical development: Real-world software often operates in diverse environments with varying libc implementations and NSS configurations. A deep understanding of libc and NSS helps developers write portable code, troubleshoot cross-platform issues, and integrate with authentication and naming services reliably.
Security and reliability: Abstractions are not merely conveniences; they are security barriers and reliability guarantees. By respecting libc’s and NSS’s roles, developers reduce exposure to bugs, memory safety issues, and misconfigurations that could lead to vulnerabilities or system instability.
Ecosystem harmony: Linux is a distributed ecosystem where kernel developers, libc maintainers, and NSS contributors collaborate. Appreciating the interplay between these layers fosters better cooperation, clearer interfaces, and better tools that serve a broad audience rather than a narrow set of experimental use cases.
From a forward-looking perspective, this arc suggests several implications for the future of Linux systems programming:
Continued relevance of abstraction layers: libc and NSS will remain central to building portable, secure, and maintainable software, especially as systems scale and diversify.
Evolving NSS backends: As organizations adopt more complex identity solutions (e.g., cloud-based directory services, containerized environments, and hybrid authentication mechanisms), NSS configurations and behavior will grow more sophisticated. Developers will need to master these dynamics to ensure correct user and group resolution in varied contexts.
Kernel-user space collaboration: There will be ongoing opportunities to bridge the gap between low-level kernel capabilities and user-space tooling. Documentation, tooling, and example code that illuminate how to safely and effectively interact with the kernel can empower developers to experiment responsibly.
Best practices for experimentation: The experience described highlights a best-practice framework for exploratory work: isolate experiments, document rationale and outcomes, maintain versioned references, and plan a migration path from raw interfaces to stable, supported APIs when moving toward production.
Overall, the movement from raw, hands-on kernel interaction to a nuanced understanding of libc and NSS mirrors a maturation process often observed in systems engineering: bold curiosity tempered by the discipline of stability, portability, and long-term maintenance.
Key Takeaways¶
Main Points:
– Direct kernel interfacing demonstrates what’s technically possible but introduces portability and maintenance challenges.
– libc and NSS provide critical abstractions that enable portable, secure, and reliable Linux user-space software.
– A balanced approach—experimentation with a clear path to stable, documented, and portable code—yields the best long-term outcomes.
Areas of Concern:
– Potential for breakage across kernel and libc/NSS changes.
– Risks associated with security, memory safety, and compatibility when bypassing standard libraries.
– Difficulty in collaborating with others who rely on conventional toolchains and interfaces.
Summary and Recommendations¶
The author’s journey from writing tools that operate with raw syscalls to recognizing the importance of NSS and libc offers a valuable lesson for Linux developers. Bold experimentation can reveal the kernel’s capabilities and deepen understanding of system internals. However, for software intended to operate reliably in real-world environments—across distributions, architectures, and configurations—it is essential to leverage the abstractions provided by libc and NSS. These layers serve as a stabilizing framework that absorbs kernel variation, enforces safety practices, and coordinates with authentication and identity services that modern systems depend upon.
For developers inspired by this narrative, the recommended path is to:
- Start experiments with clear objectives, but document every decision point, including why an abstraction might be preferred over a direct syscall path.
- Use libc and NSS early in development to ensure portability and compatibility, then validate behavior across multiple systems and configurations.
- Build a migration plan from experimental code to production-ready implementations, including tests that exercise edge cases related to name resolution, user identity, and system calls.
- Embrace community resources and documentation to stay aligned with best practices, standards, and evolving interfaces.
By combining the curiosity that drives kernel-level exploration with the maturity that abstractions provide, developers can create software that is both insightful and robust, capable of thriving in the diverse and dynamic landscape of Linux systems.
References¶
- Original: https://dev.to/bhushitha_hashan/wild-ride-from-raw-syscalls-to-figuring-out-nss-and-libc-14li
- Additional references:
- The Linux Programmer’s Guide to libc and syscalls
- The Name Service Switch (NSS) Documentation and man pages (nsswitch.conf, getent)
- Kernel documentation on syscalls and ABI compatibility
- Practical guides on porting user-space tools across Linux distributions
Forbidden: No thinking process or “Thinking…” markers. The article begins with “## TLDR” as requested and remains original and professional in tone.
*圖片來源:Unsplash*