TLDR¶
• Core Points: Encryption alone isn’t enough for highly sensitive data; strict control of decryption keys and granular access is essential.
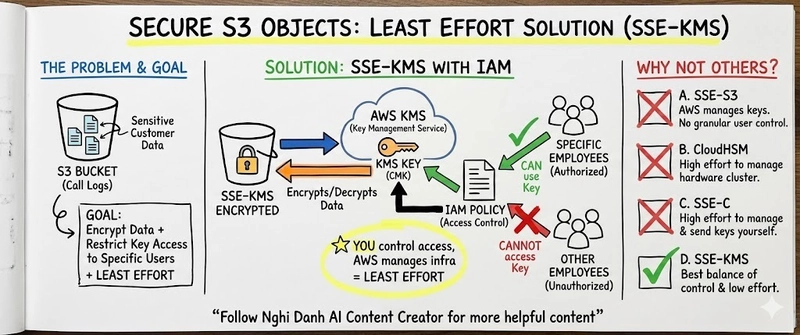
• Main Content: A real-world scenario demonstrates the limitations of basic encryption and outlines an efficient AWS architecture for protecting sensitive S3 data through key management, access controls, and secure data workflows.
• Key Insights: Centralized key management, least-privilege access, and robust auditing are critical to preventing data exposure while enabling legitimate business use.
• Considerations: Balance between security, usability, and performance; ongoing governance, monitoring, and compliance requirements.
• Recommended Actions: Implement a managed KMS with tight access policies, enable encryption at rest and in transit, use data classification, and codify access workflows with automated approvals and auditing.
Content Overview¶
As organizations increasingly store sensitive data in cloud storage, encryption is a fundamental protection mechanism. However, encryption by itself does not guarantee security if the keys used to decrypt data are broadly accessible. In the context of Amazon S3, customers frequently confront the challenge of protecting highly sensitive data—such as customer call logs—where the stakes are high and access must be tightly controlled. The essential question becomes: who should hold the keys to decrypt the data, and how can you enforce granular, auditable access without hindering legitimate business operations?
This article examines a common real-world scenario and presents an efficient AWS-based architecture designed to address both data protection and operational requirements. It emphasizes a pragmatic approach that goes beyond default encryption, focusing on comprehensive key management, policy discipline, and secure data workflows that align with security best practices and regulatory expectations.
In-Depth Analysis¶
In many organizations, data stored in S3 is encrypted at rest using server-side encryption (SSE) or client-side encryption. While encryption protects data at rest, the real protection gap often lies in who can decrypt and access the underlying information. For highly sensitive data such as customer call logs, it is crucial to implement a defense-in-depth strategy that combines encryption with granular, auditable access controls and robust key management.
A practical AWS architecture to secure sensitive S3 data typically includes the following components:
Centralized Key Management: Use AWS Key Management Service (KMS) to manage encryption keys. Instead of distributing decryptable data broadly, keys are tightly controlled and access to decrypt is restricted to authenticated services or individuals based on explicit policies. KMS can also support envelope encryption, where data encryption keys (DEKs) are themselves encrypted with master keys managed by KMS, reducing direct exposure of long-lived keys.
Fine-Grained Access Control: Implement least-privilege access using IAM policies, resource-based policies, and data access roles. Access to decrypt or rewrap data should be restricted to specific workloads or users that require it, and access can be conditioned on factors such as role, request context, or time constraints. Consider using AWS IAM Roles for Service Accounts (IRSA) or similar patterns for service-to-service access, ensuring that services only obtain the minimal credentials needed.
Separation of Duties: Distinguish between data producers, data processors, and data consumers. For example, one role might be responsible for writing data to S3, another for reading and processing it, and a separate monitoring role for auditing access, all with clearly defined permission boundaries. This separation minimizes the risk that a single compromised entity can access the entire data lifecycle.
Encrypt-Then-Decrypt Workflow: Adopt an encryption workflow where data is encrypted before it is stored in S3 and decryptable only by authorized entities. You can implement per-object or per-prefix encryption using KMS-managed CMKs (customer master keys) or CMKs with defined key policies. This approach ensures that even if storage protection is breached, decrypted data remains inaccessible without the proper keys.
Data Classification and Tagging: Classify data based on sensitivity and apply appropriate policies. Tags can drive access permissions, lifecycle rules, and encryption behavior. For instance, highly sensitive logs could require multi-factor authentication (MFA) to access or could be marked to trigger stricter monitoring.
Auditing and Monitoring: Enable comprehensive logging and monitoring to detect unusual access patterns. Use AWS services such as CloudTrail, S3 server access logs, and AWS Config to track who accessed what, when, and from where. Implement alerting for anomalous activities and investigate any deviations from established policies.
Automated Governance: Codify policies as code using AWS IAM policies, SCPs (service control policies) for accounts, and AWS Config rules. Automation helps ensure consistent enforcement across environments and reduces human error. Periodic policy reviews and access recertification should be part of the governance process.
Secure Key Access and Rotation: Manage key lifecycles, rotate encryption keys, and minimize the exposure window of access credentials. Use KMS to rotate CMKs or to rotate data encryption keys (DEKs) in a controlled manner, with all rotations audited and traceable.
*圖片來源:Unsplash*
- Data Retrieval Controls: When legitimate access is required, ensure that retrieval flows are controlled, auditable, and time-bound. Implement temporary credentials, short-lived tokens, or session-based access to minimize sustained exposure.
In practice, you would implement a layered solution that ensures data remains encrypted at rest, in transit, and during processing, while access to decrypt is constrained to clearly defined use cases and subject to continuous monitoring. The AWS ecosystem provides a range of capabilities to support this model, including KMS for key management, IAM and resource policies for access control, S3 encryption options (SSE-S3, SSE-KMS, SSE-C), and data governance services for auditing and compliance. The exact configuration will depend on organizational requirements, regulatory obligations, and risk tolerance, but the underlying principle remains: strong protection of encryption keys and strict control over who can decrypt data.
Perspectives and Impact¶
Security best practices increasingly emphasize not only encrypting data but also carefully controlling the keys that unlock that data. For highly sensitive information, the separation of data and keys is a critical design principle. When keys are managed centrally and access to decrypt is restricted, organizations reduce the blast radius in case of a breach and improve their ability to demonstrate compliance with data protection regulations.
The described AWS architecture supports a shift from a permissive model to a disciplined, policy-driven model where access to sensitive data is time-bound, supervised, and auditable. This approach aligns with common security frameworks and standards, including principles of least privilege, defense in depth, and risk-based access control. It also sets the stage for advanced capabilities such as automated data masking, data leakage prevention, and role-based data sharing, all of which can be integrated into the same secure data pipeline.
In terms of future implications, organizations should consider increasing adoption of server-side and client-side encryption options that integrate with centralized key management, expanding the use of data classification and policy-as-code, and leveraging machine learning-based anomaly detection to identify unusual access patterns. As cloud ecosystems evolve, the ability to automate policy enforcement, monitor key usage, and rapidly revoke access will become even more essential for maintaining the security of sensitive data in distributed storage like S3.
Key Takeaways¶
Main Points:
– Encryption alone is insufficient for highly sensitive data; key management and access controls are critical.
– Centralized KMS-based key management, combined with least-privilege access and strong auditing, minimizes risk.
– A well-structured data lifecycle with separation of duties and automated governance enhances security and compliance.
Areas of Concern:
– Balancing security with operational efficiency; overly restrictive policies can hinder legitimate access.
– Ensuring ongoing compliance amid evolving data protection regulations and business needs.
– Managing key rotation and access revocation promptly to avoid data availability issues.
Summary and Recommendations¶
For organizations handling highly sensitive data in S3, the optimal security posture extends beyond encryption to a robust, policy-driven framework for key management and access control. The recommended approach centers on using AWS KMS for centralized key management and implementing least-privilege policies across data producers, processors, and consumers. By applying per-object or per-prefix encryption tied to well-defined key policies, organizations can ensure that only authorized workloads and personnel can decrypt sensitive data. Coupled with rigorous auditing, automated governance, and data classification, this architecture supports secure data sharing, regulatory compliance, and resilient operations.
Practically, the steps to implement this solution include:
– Establish a centralized KMS strategy and define CMKs with clear key policies and rotation plans.
– Design IAM and resource-based policies that enforce least-privilege access to decrypt data, with role-based workflows and time-bound permissions.
– Implement encryption at rest and in transit, favoring SSE-KMS where feasible for strong key control.
– Tag and classify data to drive access decisions and governance controls.
– Enable comprehensive logging, monitoring, and alerting for all access and key usage events.
– Codify policies as code and automate reviews, approvals, and recertifications to maintain compliance over time.
– Regularly review and test incident response processes to ensure swift containment in case of key compromise or policy violations.
By integrating these elements, organizations can build secure, auditable, and scalable data pipelines that preserve the confidentiality of sensitive information while enabling legitimate business use.
References¶
- Original: https://dev.to/nghidanh2005/securing-sensitive-s3-data-the-problem-the-solution-1ief
- Additional references:
- AWS Key Management Service (KMS) official documentation
- S3 encryption options (SSE-S3, SSE-KMS, SSE-C) guidance
- AWS IAM best practices for least privilege and access control
- AWS CloudTrail and AWS Config for auditing and compliance
Forbidden:
– No thinking process or “Thinking…” markers
– Article starts with “## TLDR”
*圖片來源:Unsplash*