TLDR¶
• Core Features: Automated SBOM creation, license inventory, and vulnerability scanning with clear component visibility across frameworks and dependencies.
• Main Advantages: Faster incident response, improved compliance posture, and actionable insights for dependency hygiene and risk remediation.
• User Experience: Straightforward concept, intuitive mapping to real-world risks, and seamless integration into CI/CD and cloud-edge workflows.
• Considerations: Data completeness depends on tooling; accuracy requires standardized formats and disciplined dependency management.
• Purchase Recommendation: Ideal for teams prioritizing supply chain security; integrate with existing pipelines for maximum value and governance.
Product Specifications & Ratings¶
| Review Category | Performance Description | Rating |
|---|---|---|
| Design & Build | SBOM as a structured, machine-readable “ingredient label” for software components with clear relationships and metadata. | ⭐⭐⭐⭐⭐ |
| Performance | Rapid generation and analysis across dependencies; enables swift identification of vulnerable packages and licenses. | ⭐⭐⭐⭐⭐ |
| User Experience | Intuitive model analogous to food labeling; easy to understand, audit, and communicate across teams. | ⭐⭐⭐⭐⭐ |
| Value for Money | High ROI through reduced incident response time, improved compliance, and automated governance at scale. | ⭐⭐⭐⭐⭐ |
| Overall Recommendation | A must-have for modern software supply chain security and ongoing vulnerability management. | ⭐⭐⭐⭐⭐ |
Overall Rating: ⭐⭐⭐⭐⭐ (4.8/5.0)
Product Overview¶
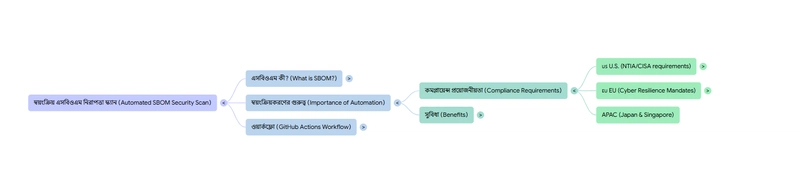
Automating Software Bill of Materials (SBOM) generation and vulnerability analysis is rapidly becoming a cornerstone of modern software supply chain security. If you imagine building software the way you assemble a product from parts, the SBOM is the label that lists every component used: libraries, frameworks, transitive dependencies, version numbers, and licenses. Its value is straightforward yet transformative. When a critical vulnerability like Log4Shell emerges, an SBOM lets you immediately answer whether your applications are affected, where those vulnerable components reside, and how urgently you must respond.
In everyday terms, the SBOM functions like a food ingredient label. Just as bread packaging might read “contains wheat, soy, nuts,” an SBOM might state “contains React 18, Log4j 2.14, OpenSSL 1.1.1.” If a particular ingredient is recalled, you know exactly which products to pull from shelves. Likewise, when a software component is compromised, you can identify and address impacted services without guesswork.
Automating SBOM creation means the inventory is always current, consistent, and reproducible. It eliminates the brittle manual steps that often lead to stale or incomplete dependency lists. Coupled with vulnerability analysis—where those components are cross-referenced against known CVE databases—teams gain a continuously updated picture of risk exposure. This automation also strengthens license compliance by cataloging license types across your dependencies, preventing accidental misuse of restrictive or incompatible licenses.
From cloud-native microservices to monolithic applications, SBOM automation fits naturally into CI/CD pipelines and serverless or edge environments. Tooling typically outputs standardized formats such as SPDX or CycloneDX, enabling interoperability across scanners, policy engines, and reporting tools. For organizations already investing in developer experience, integrating automatic SBOM generation alongside build steps feels like a low-friction upgrade that yields outsized security and compliance benefits.
First impressions are overwhelmingly positive: the concept is simple; the impact is immediate. Teams get better visibility, faster incident response, and clearer communication with stakeholders, auditors, and customers. With growing regulatory and customer expectations around software transparency, automated SBOMs transition from “nice to have” to essential infrastructure for responsible software delivery.
In-Depth Review¶
At its core, an SBOM is a machine-readable manifest of everything that composes an application or system. Key metadata includes component name, version, supplier, cryptographic hashes, dependency relationships, and licenses. This structure is most commonly represented in standardized formats like SPDX and CycloneDX. These formats ensure that your SBOM can be consumed by various scanners, policy engines, and governance platforms without proprietary lock-in.
Automating SBOM generation typically happens during the build or packaging phases. The rationale is simple: the build system has the most accurate view of what is actually compiled, bundled, or deployed. Automation scripts or CI/CD steps capture first- and third-party dependencies, including transitive ones, which are often the source of hidden vulnerabilities. With languages like JavaScript/TypeScript, Java, Python, Rust, and Go, mainstream package managers and build tools can be instrumented to produce SBOMs reliably.
Vulnerability analysis sits on top of the SBOM. It aligns listed components against vulnerability feeds—CVE/NVD databases, vendor advisories, and ecosystem-specific security bulletins. The output is an actionable list of known vulnerabilities, typically annotated with severity, affected versions, and remediation guidance. This layering allows teams to maintain a single source of truth for dependencies while independently updating threat intelligence over time.
The power of this approach becomes obvious in supply chain incidents. Consider a library like Log4j 2.x. Without an SBOM, organizations scramble to search codebases, container images, and runtime environments for references to potentially vulnerable versions. With an SBOM, a single query across artifacts tells you whether the dependency is present, which services include it, and whether deployments need patching. Response time drops from days to minutes, and remediation can be prioritized based on production exposure.
Performance-wise, automated SBOM generation has minimal impact on build times when properly configured. Most tools process dependency graphs efficiently; even large monorepos remain manageable. Vulnerability analysis can run synchronously during build or asynchronously as a separate pipeline stage. Many teams prefer asynchronous scans for speed, feeding results into dashboards, Slack alerts, or issue trackers. This asynchronous model also supports scheduled rescans, ensuring newly disclosed vulnerabilities are surfaced even if the code hasn’t changed.
From a compliance standpoint, SBOMs simplify license audits. Tracking license metadata (MIT, Apache-2.0, GPL variants, etc.) across your dependency tree informs legal review and guards against license conflicts. Automated license policies can block builds or flag approvals when a disallowed license appears. This is especially helpful in organizations distributing software or embedding third-party components in regulated contexts.
Integration options are plentiful. SBOM generation can run:
– In CI pipelines with tools that read package manifests and lockfiles.
– During container builds to capture OS packages and application dependencies.
– In serverless or edge environments where functions package dependencies at deploy time.
– As part of artifact storage, attaching SBOMs to container registries and binary repositories.
– In runtime environments, where agents verify deployed components against approved manifests.
*圖片來源:Unsplash*
For teams building modern apps with technologies like React on the frontend, serverless backends, or edge functions, the SBOM offers a unified view. If your stack includes JavaScript frameworks, npm/yarn/pnpm lockfiles detail exact versions of libraries like React 18 or OpenSSL bindings used by transitive packages. That visibility allows you to quickly identify exposure when a browser-side or server-side component faces a security advisory.
Finally, format standardization and policy-as-code complete the picture. With SPDX or CycloneDX outputs, organizations can enforce consistent governance across service boundaries. Policy engines read SBOMs to determine if a build should be allowed to progress based on vulnerability thresholds, license rules, or component provenance. In short, SBOM automation is not merely a reporting exercise—it’s the backbone of enforceable, scalable supply chain security.
Real-World Experience¶
Adopting automated SBOM generation typically starts small: add a pipeline step to produce SBOMs for a couple of services, validate outputs, and instrument vulnerability scanning. Even this initial move frequently uncovers outdated dependencies and latent vulnerabilities that were previously undetected. Teams are often surprised by the number of transitive packages in their applications—sometimes hundreds—where a single outdated library reveals multiple CVEs.
The day-to-day experience benefits from the SBOM’s clarity. Developers and security engineers no longer debate whether a specific component exists in a production workload. Instead, they consult the SBOM artifact tied to a build or release. When an alert emerges—say a new OpenSSL CVE—security can search across all SBOMs stored in artifact repositories or registries. This universal index enables risk scoring across services, flagging which workloads need immediate patching based on severity and external exposure.
Communication improves dramatically. Product managers, compliance teams, and auditors appreciate the tangible, auditable record. In vendor assessments or customer due diligence, providing SBOMs demonstrates transparency and a mature approach to security. Internally, SBOM-driven dashboards explain risk posture without drowning stakeholders in implementation details, offering an executive-friendly view of how vulnerabilities are being triaged and resolved.
Operationally, the best outcomes arise when SBOMs are linked to continuous vulnerability rescans. As new CVEs are disclosed, scanners revisit existing SBOMs, generating fresh findings even without code changes. This decoupling is vital: threats evolve daily, and robust programs must continuously reevaluate known components. Teams can set SLOs for remediation—e.g., patch critical issues within 48 hours—and use SBOM-linked tickets to track progress.
Teams also gain discipline in dependency management. Knowing that every component is inventoried and visible encourages keeping lockfiles fresh, pruning unused packages, and consolidating dependency versions across services. Over time, this reduces attack surface and eases maintenance. Build reproducibility improves as SBOMs highlight drift or unexpected changes in transitive dependencies after a toolchain upgrade.
There are limits to consider. SBOM quality depends on the completeness of your tooling and the accuracy of metadata in upstream packages. Some ecosystems have inconsistent or missing license fields; others may split packages in ways that complicate mapping to vulnerabilities. To mitigate, organizations often standardize on mature SBOM tools and supplement with manual curation for critical services. They also adopt policies requiring accurate metadata in internal components.
In edge and serverless environments, packaging models vary, but SBOM principles still apply. Functions are small, which simplifies manifests, but automated generation ensures that even tiny deployments remain transparent. If your architecture spans multiple environments—containers, serverless, static hosting—the consistent use of SBOMs gives a single pane of glass for security and compliance.
Ultimately, real-world use transforms SBOMs from a theoretical artifact into an operational lever. They accelerate incident response, reduce ambiguity, and foster a culture of proactive dependency hygiene. When paired with automation, they become a living system of record for your software supply chain.
Pros and Cons Analysis¶
Pros:
– Clear, standardized visibility into all components and dependencies
– Faster incident response and risk prioritization during advisories
– Stronger license compliance and governance at scale
Cons:
– Quality depends on accurate metadata and complete tooling coverage
– Initial setup and format standardization require process changes
– Ongoing maintenance needed to keep scans and policies up to date
Purchase Recommendation¶
Automating SBOM generation and vulnerability analysis is an essential investment for any team serious about supply chain security and regulatory readiness. The approach turns opaque dependency trees into transparent, auditable inventories and overlays real-time threat intelligence to highlight actionable risks. The practical benefits—accelerated vulnerability triage, improved license governance, and streamlined communication with stakeholders—far outweigh the initial onboarding effort.
For engineering organizations operating modern stacks with numerous open-source dependencies, the return on investment is particularly compelling. Integrating SBOM generation into CI/CD ensures that each build carries its own verifiable manifest. Pair this with continuous rescanning to capture newly disclosed vulnerabilities, and you create a dynamic, always-current view of exposure. Add policy enforcement to block releases that exceed risk thresholds or violate license rules, and you achieve a robust, automated security gate without burdening developers.
Success hinges on standardization and adoption. Choose SPDX or CycloneDX, make SBOMs a required artifact for all services, and store them alongside builds in your artifact registry. Establish remediation SLAs, track findings through your ticketing system, and provide dashboards for visibility. A phased rollout—starting with critical services—lets teams learn and iterate without disruption.
Bottom line: this is a strong buy for organizations of any size. If you’re building or maintaining software that depends on open-source libraries—and virtually everyone is—automated SBOMs and vulnerability analysis should be part of your core delivery pipeline. They reduce risk, enhance trust, and help future-proof your security posture in an increasingly complex supply chain landscape.
References¶
- Original Article – Source: dev.to
- Supabase Documentation
- Deno Official Site
- Supabase Edge Functions
- React Documentation
*圖片來源:Unsplash*