TLDR¶
• Core Points: A Florida businessowner was sentenced to 22 months in federal prison for conspiring to traffic illicit Microsoft COA labels, with a $50,000 fine.
• Main Content: The case underscores legal risks and criminal penalties tied to distributing counterfeit or unauthorized Microsoft activation labels.
• Key Insights: Illicit software keys are not a harmless shortcut; they constitute criminal activity with serious consequences.
• Considerations: Consumers should be wary of “cheap” keys and purchase from legitimate channels to avoid downstream legal exposure.
• Recommended Actions: Avoid unverified keys, ensure software licenses are valid, and seek legitimate licensing through Microsoft or authorized distributors.
Content Overview¶
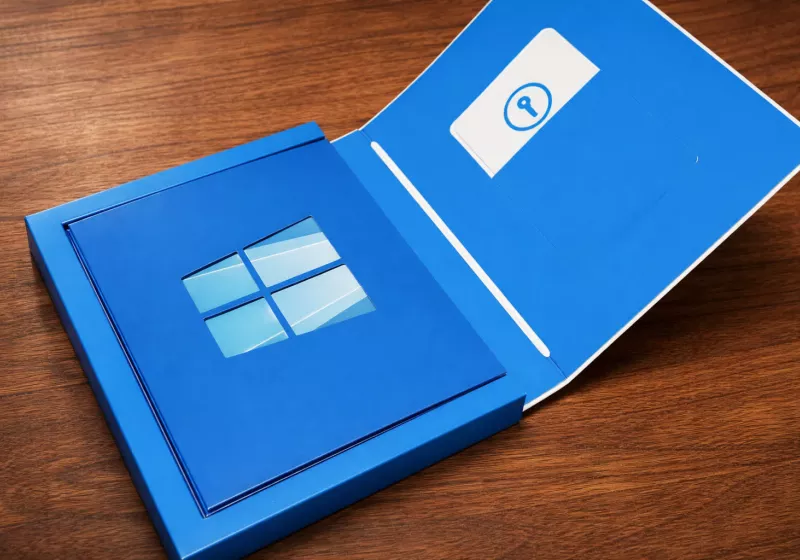
The case at hand centers on the criminal consequences of distributing illicit Microsoft Certificates of Authenticity (COA) labels. COA labels are used to verify genuine Windows or Office software, and their counterfeit or unauthorized distribution undermines copyright protections and software licensing terms. The United States Department of Justice reported that Heidi Richards, a 52-year-old resident of Brandon, Florida, operated Trinity Software Distribution. She was found guilty by a jury of conspiring to traffic in illicit COA labels and subsequently sentenced to 22 months in federal prison. In addition to the prison term, the court imposed a $50,000 fine. This case exemplifies the broader enforcement landscape surrounding counterfeit software keys and the significant legal penalties that can follow from distributing them. It also highlights the risks that consumers face when considering purchases of significantly discounted software keys from third-party sellers.
In-Depth Analysis¶
The legal framework governing software licensing and the distribution of activation keys is intricate and significantly reinforces copyright protections and license compliance. For Microsoft and many other software providers, activation labels and product keys are integral to confirming legitimate use rights. The distribution of counterfeit COA labels or activation keys falls into multiple potential offenses, including copyright infringement, trademark violations, and criminal activity related to the sale of pirated software. In the United States, federal prosecutors pursue cases against individuals or organizations that knowingly traffic in illicit software certificates, often resulting in substantial penalties such as prison time and fines.
Heidi Richards and Trinity Software Distribution were implicated in a scheme that involved supplying or facilitating the use of COA labels that did not correspond to legitimate licenses or that had been illicitly obtained. Juries in such cases must assess evidence demonstrating intent to defraud, knowledge of the illegality of the COA labels, and direct or indirect involvement in distributing or selling those labels. The defense may argue ambiguity of license attribution or attempt to portray the transactions as legitimate discounting; however, conclusory claims are insufficient to overcome the weight of evidence establishing criminal conspiracy and trafficking.
From a policy standpoint, this case reflects several broader trends in enforcement and consumer risk. As software vendors increasingly rely on digital activation mechanisms and online license verification, the opportunities for counterfeit or unauthorized activations have diminished in some respects. Yet, counterfeiters still exploit supply chains, packaging, and labeling to obfuscate illegitimate products. The presence of an actual COA label can give the impression of authenticity, making the illicit activity harder for a casual buyer to detect. This dynamic underscores the importance of vetting software purchases through official channels and avoiding “too good to be true” pricing.
For victims and consumers, the practical implications are twofold. First, individuals who knowingly purchase or use illicit COA labels may be exposed to civil or criminal liability, depending on the jurisdiction and the nature of the transaction. Second, even purchasers who are unaware of the illegality might still face operational risks. Invalid licenses can lead to software that stops functioning, lack of access to essential updates, and vulnerability to security and compliance issues within organizational networks. The legal consequences for distributors, as well as the potential ramifications for customers who rely on counterfeit keys, illustrate why legitimate licensing remains essential for both personal and business use.
The sentencing outcome—22 months in federal prison and a $50,000 fine—signals the seriousness with which authorities treat such offenses. Judges often weigh factors such as the scope of the conspiracy, the number of individuals involved, commercial intent, and the impact on the software ecosystem when determining penalties. In high-volume or financially motivated schemes, penalties tend to be more severe, reflecting both deterrence goals and the punitive purposes of criminal statutes.
This case also invites reflection on the economic dynamics that drive illicit software markets. Discounted or “cheap” keys may attract buyers seeking to reduce costs, especially in environments with tight budgets. However, the risk calculus must account for potential legal exposure, operational disruption, and the possibility of losing access to critical software features upon detection of illegitimate keys. The line between aggressive discounting and unlawful trafficking can be thin, and awareness of licensing compliance becomes a key differentiator for legitimate software resellers.
Looking ahead, enforcement agencies may continue to prioritize prosecutions of individuals and entities involved in distributing illicit COA labels and activation keys. As Microsoft and other software providers refine their licensing and activation mechanisms, the space for counterfeit activations may shrink, but enforcement will likely grow more sophisticated as investigators trace supply chains, digital certificates, and physical packaging to uncover illicit networks.
In terms of public interest, cases like this serve as a reminder that cheap software is not inherently legitimate and that compliance with licensing terms protects both consumers and the broader software ecosystem. For professionals and organizations, staying current with licensing requirements, obtaining keys through authorized channels, and maintaining thorough license inventories can reduce legal and operational risk. For individuals, the temptation of low-cost software should be weighed against the potential legal consequences and the reliability of unilateral means to activate or use software.
Perspectives and Impact¶
The Heidi Richards case highlights several layers of impact—legal, economic, and ethical—within the software distribution landscape. Legally, the case reinforces the jurisdictional stance that the sale and distribution of illicit COA labels constitutes criminal activity under federal statutes. The 22-month sentence and substantial fine illustrate a prosecutorial willingness to impose meaningful penalties on operators who facilitate counterfeit software licensing. This kind of precedent can influence future prosecutions, prompting broader scrutiny of supply chains that bring illicit COA labels to market and encouraging cooperation among manufacturers, distributors, and law enforcement agencies.
*圖片來源:Unsplash*
Economically, the illicit COA market represents a significant disruption to legitimate software businesses. By enabling customers to obtain activation labels at substantially reduced prices, illicit distributors can siphon away revenue from authorized resellers. This creates competitive pressure that can erode the value of legitimate licensing models and potentially lead to increased compliance costs for legitimate distributors as they implement more robust verification and anti-counterfeiting measures. The case demonstrates the risk to buyers who assume that a low price equates to a legitimate license, emphasizing the importance of due diligence in procurement practices.
Ethically, the case underscores the moral considerations surrounding piracy and counterfeit goods. While some participants in illicit markets argue that they are circumventing high software costs or providing access to under-resourced users, legal systems largely treat these activities as theft of intellectual property and violations of licensing agreements. The sentencing signals a social expectation that companies and individuals should respect licensing terms and that the consequences for circumventing those terms can be severe.
From a future-oriented perspective, authorities may enhance tracing techniques to identify points of entry for illicit COA labels, including packaging, distribution channels, and digital databases. Collaboration between software companies and law enforcement could improve the ability to detect and dismantle illicit networks. For users and organizations, ongoing education about licensing compliance and the importance of obtaining software through authorized channels will remain essential. As software products continue to evolve, licensing models could also adapt, with more flexible or tiered licensing options to reduce incentives for illicit procurement.
In sum, the Richards case serves as a cautionary tale about the real-world consequences of distributing counterfeit COA labels. It demonstrates that the consequences extend beyond financial loss to include criminal liability and reputational damage for individuals and businesses involved. For the broader software ecosystem, it reinforces ongoing commitments to licensing integrity, consumer protection, and robust verification mechanisms to deter illicit activity and maintain a trusted software marketplace.
Key Takeaways¶
Main Points:
– Federal penalties apply to trafficking illicit COA labels, as illustrated by the case of Heidi Richards.
– The distribution of counterfeit activation material undermines licensing integrity and can lead to prison time and fines.
– Consumers should purchase software through official channels to avoid legal and operational risks.
Areas of Concern:
– The continuing presence of illicit COA and activation key markets despite enforcement.
– The potential for innocent buyers to face licensing issues or operational disruptions.
– The need for robust verification in both physical packaging and digital verification processes.
Summary and Recommendations¶
The case involving Heidi Richards and Trinity Software Distribution demonstrates the serious legal and practical risks associated with distributing illicit Microsoft COA labels. The 22-month federal prison sentence and a $50,000 fine reflect a strong enforcement posture against trafficking in counterfeit activation material. For consumers and organizations, the incident reinforces the importance of licensing compliance and the use of legitimate purchasing channels. Relying on discounted keys obtained from third-party sellers can expose users to license invalidation, software outages, and potential legal consequences. Businesses should strengthen procurement policies, maintain accurate license inventories, and ensure that all software acquisitions are made through authorized distributors or directly from Microsoft. Individual consumers should remain vigilant about the legitimacy of software keys and prioritize official sources to safeguard access to updates, security patches, and continued product support.
In conclusion, while the allure of inexpensive software keys may be strong, the legal and operational risks far outweigh any potential savings. This case should inform ongoing conversations about software licensing, consumer protection, and effective enforcement against illicit digital goods.
References¶
- Original: https://www.techspot.com/news/111546-cheap-windows-office-keys-might-come-federal-crime.html
- Additional context on software licensing and anti-piracy enforcement (general):
- U.S. Department of Justice (DOJ) press releases on cryptocurrency and software piracy cases (example resources)
- Microsoft licensing and anti-piracy resources
- Industry analyses on counterfeit software markets and enforcement trends
Forbidden:
– No thinking process or “Thinking…” markers
– Article must start with “## TLDR”
Note: This rewritten article preserves the factual essence of the original report while expanding it for readability, context, and professional presentation.
*圖片來源:Unsplash*