TLDR
• Core Points: HBO’s It: Welcome to Derry, from Andy and Barbara Muschietti and Jason Fuchs, is nearing renewal with strong indications of a seco…
If You’re Not Watching Frieren, You’re Missing Out on the Best Fantasy Anime in Ages
TLDR
• Core Points: Frieren: Beyond Journey’s End Season 2 is shaping up as a must-watch fantasy anime for 2026, offering depth, world-building, and e…
‘Wildly productive weekend’: Former Amazon exec’s vibe coding post sparks debate over viral AI to…
TLDR
• Core Points: A startup leader and former Amazon Worldwide Consumer CEO shared a weekend vibe-coding project, prompting discussion about AI deve…
Satya Nadella’s New Metaphor for the AI Age: We Are Becoming “Managers of Infinite Minds”
TLDR
• Core Points: Microsoft CEO Satya Nadella reframes AI leadership as guiding “infinite minds,” building on classic tech metaphors seen at Davos. …
Global App Spending Surpasses Mobile Games for First Time as AI Assistants Drive Growth
TLDR
• Core Points: Global app spending reached about $167 billion in 2025, a 10.6% year-over-year rise, with non-game apps leading the growth as AI a…
Podcast: Best of CES 2026 – Soundbars, Wireless Speakers, TVs & Projectors
TLDR
• Core Points: CES 2026 showcased standout soundbars, wireless speakers, TVs with high dynamic range, and new projector technologies delivering i…
Bill to Tax Short-Term Rentals Returns in Washington State, Alongside Airbnb Opposition
TLDR
• Core Points: Washington state considers a 4% local tax on short-term rentals, allowing counties and municipalities to implement it; the measure…
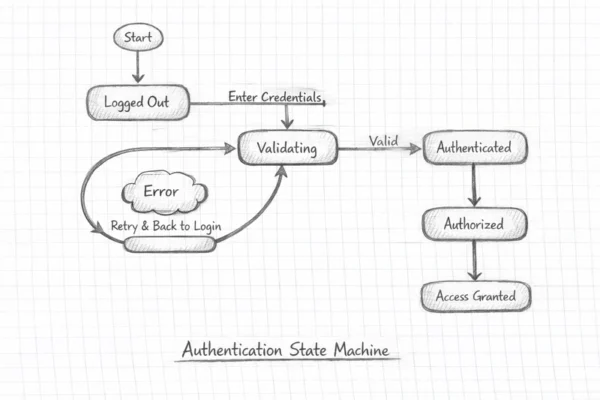
From Workflows to Autonomous Agents: How AI Agents Actually Work
TLDR
• Core Points: AI agents differ in how they decide and sequence actions; some follow rigid workflows, others generate autonomous steps toward a g…
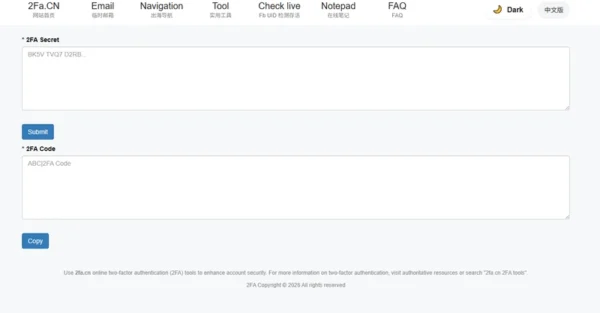
How Developers Test 2FA Without Installing Authenticator Apps
TLDR
• Core Points: 2FA testing can be streamlined without repeatedly installing authenticator apps by using secure test secrets, mock flows, and auto…
前所未見的 Linux 惡意軟體:遠比常見型態更為高級與全面
TLDR
• 核心重點:新型 Linux 惡意軟體具備廣泛且高階的能力組合,顯示攻擊向量與持久性策略的顯著提升
• 主要內容:該惡意軟體結構嚴謹,具多模態功能,使取證與防護難度增加
• 關鍵觀點:其設計涵蓋持久性、隱蔽性與自我保護機制,對現有防護策略提出更高要求
• 注意事項:需關注供應鏈風險與受影…