TLDR
• Core Points: Eclectic chic blends diverse styles, textures, and eras into cohesive spaces; TikTok accelerates trend adoption and inspiration; d…
Bullet Journal vs Junk Journal: What’s the Difference and Which One Is Right for You?
TLDR
• Core Points: Bullet journals organize tasks with rapid logging; junk journals emphasize creative, tactile scrapbooking and found materials for …
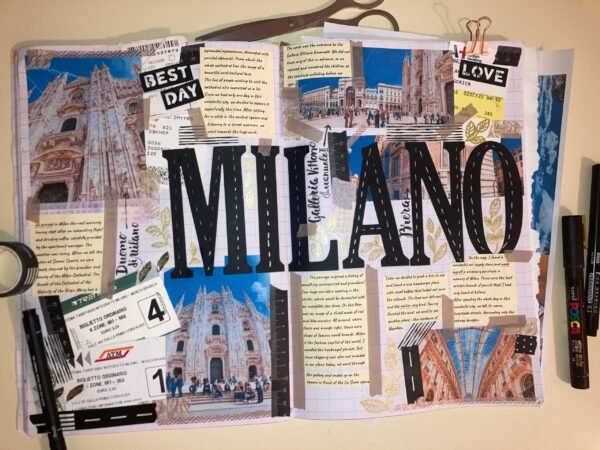
50 Epic Travel Vacation Junk Journal Ideas
TLDR
• Core Points: Creative ways to preserve travel memories using journals, ephemera, and personal storytelling.
• Main Content: A curated list of…
21 Stunning Wedding Trends to Embrace in 2026
TLDR
• Core Points: Expect bold color palettes, sustainable planning, intimate guest experiences, and personalized details shaping weddings in 2026. …
Key Elements of Effective Laboratory Design and Build
TLDR
• Core Points: Proper safety, ventilation, layout, and utilities are essential; thoughtful planning reduces risk, improves workflow, and ensures …
50 Bible Journaling Prompts to Inspire Reflection, Creativity, and Faith
TLDR
• Core Points: Practical prompts encourage introspection, creativity, and spiritual growth through Bible journaling.
• Main Content: A curated …
One-Word Travel Captions: The Perfect Instagram Boost
TLDR
• Core Points: Short, punchy one-word captions can elevate travel posts, complement visuals, and invite engagement without clutter.
• Main Conten…
How to Decorate a Front Porch for Spring: 7 Gorgeous Ideas
TLDR
• Core Points: Refresh your porch with seasonal color, greenery, statement accents, and practical textures to create inviting curb appeal.
• Main…
100 Gorgeous Waterfall Captions for Instagram and A Practical Guide to Waterfall Adventures
TLDR
• Core Points: A curated list of 100 waterfall-themed Instagram captions plus a practical guide to planning waterfall adventures.
• Main Conten…
When Password Managers Can’t Guarantee Privacy: How Server Breaches Could Expose Your Vaults
TLDR
• Core Points: Password managers’ zero-knowledge claims aren’t absolute; server breaches can compromise data, requiring robust, layered security …